 Considerations for local security of Exchange 2010 servers
Considerations for local security of Exchange 2010 servers
03 Mar 2010 01:03:46 am
When designing/deploying Exchange within a dispersed environment with segregated Exchange or Active Directory administration its important to consider the functionality of Role Based Access Control (RBAC) within Exchange and the function of the Trusted Subsystem. This is directly applicable to how Local Administrators are defined for all Exchange Servers within the environment.
As youll find, all commands that are executed in either the Exchange Management Shell or the Exchange Management Console are not executed under the security context of your user account. Instead the RBAC components of Exchange take the commands and evaluate it against the Role Group(s) that you have been assigned and any policies that have been granted. If authorized to do so the commands are then executed against Windows, AD or Exchange under the security context of the Exchange server, a member of the Exchange Trusted Subsystem.
The Exchange Trusted Subsystem is a highly privileged universal security group that has access to read or modify all Exchange related objects and attributes within Active Directory, effectively making the Exchange Trusted Subsystem an organization-wide Exchange Super user. Because of this local administrator privileges over all of your Exchange servers should be highly restricted to only the most trusted administrators in your organization.
Effectively speaking, this means that anyone that has local administration privileges over a single Exchange server within your organization should be considered, by extension, a full Exchange Organization Administrator as well as Local Administrator against all other Exchange servers.
Erik Szewczyk
By : Erik | Category: Exchange | Comments [ [50]] | Trackbacks [0]
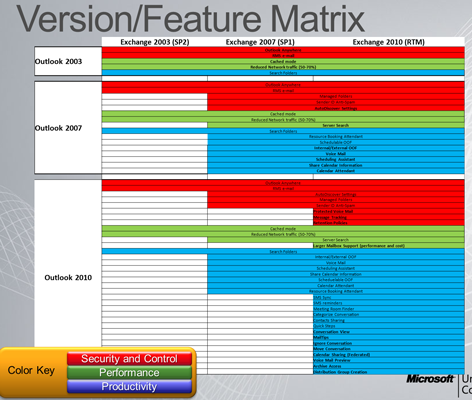
 Exchange 2003-2010 with Outlook 2003-2010 feature matrix
Exchange 2003-2010 with Outlook 2003-2010 feature matrix
30 Oct 2009 04:58:34 pm
Microsoft has released a little more information regarding the functionality of the various supported versions of outlook with various versions of Exchange. Here is an image to keep handy:
By : Erik | Category: Exchange | Comments [ [63]] | Trackbacks [0]
11 Mar 2009 10:59:46 pm
I know Im way past due on posting, Ive been spending a good deal of time preparing for E14 (and hopefully when the time is right some E14 content to post)!
Despite the CAPTCHA I put in place nearly a year ago Ive had a good deal of ongoing comment SPAM on the blog. I dont understand why someone would repeatedly lurk on my blog, often for an hour or more, posting their comment SPAM. Especially after they see all their comments suddenly disappear an hour later when I execute a quick SQL one-liner wiping out the nuisance. Youd think after the first dozen or so times they would figure it out and stop wasting their time. To put an end to this Ive started moderating all comment posts, so nothing will appear until approved.
Thanks for your patronage,
Erik
By : Erik | Category: General | Comments [ [50]] | Trackbacks [0]
 New updates to the 2008 CMS Web OAB generation issues
New updates to the 2008 CMS Web OAB generation issues
25 Aug 2008 01:14:54 am
Good news from our friends at Microsoft. They are continuing to test & update their patch to this issue (which as I mentioned already requires some changes to the way the shares are created).
Currently the plan is to release an interim fix available for SP1 RU3, and to incorporate the fix to an upcoming SP1 RU.
NOTE: as of now they are not planning on making the fix available to any builds prior to SP1 RU3, so make sure you update now so you can take advantage of this fix when its released.
Cheers,
Erik Szewczyk
By : Erik | Category: Exchange | Comments [ [130]] | Trackbacks [0]
 An update to the Server 2008 Web OAB/CMS issues
An update to the Server 2008 Web OAB/CMS issues
13 Aug 2008 08:21:03 pm
Ive been working with the folks @ MSFT on this issue and figured I would post a brief update.
The Exchange code is getting modified to pass a 503 struct which allows them to pass the name of the node the share should be created against (in this case \\nodename as well as \\cmsname).
There is a fix and it is currently undergoing testing, but has not been released as of yet.
Erik
By : Erik | Category: Exchange | Comments [ [162]] | Trackbacks [0]



